The software development landscape has reached a critical inflection point. As organizations race to deliver features faster than ever, cyber threats have evolved to exploit the very speed that gives companies their competitive edge. The sobering reality? Dev.to reports that time-to-exploit in 2026 is now under 24 hours, while traditional patch cycles still take days or weeks.
This isn’t just a technical challenge—it’s an existential business risk. If you fail to integrate security into development velocity, you end up choosing between speed and safety. And in practice, that false choice usually leads to either stagnant products or costly breaches.
The answer lies in DevSecOps: the seamless integration of security into every phase of the development lifecycle. But here’s what most guides won’t tell you—many DevSecOps implementations are still broken because they focus on tools, not workflow design.
What are DevOps Practices?
Before we dive into the “Sec” part of DevSecOps, we must understand the foundation. DevOps practices are a set of principles designed to break down the silos between development and operations teams, fostering a culture of collaboration and automation.
But what are the 7 DevOps practices that form this foundation?
- Continuous Integration (CI): Regularly merging code changes into a central repository.
- Continuous Delivery (CD): Automatically preparing code changes for a release to production.
- Microservices Architecture: Building applications as a suite of small, independent services.
- Infrastructure as Code (IaC): Managing and provisioning infrastructure through code.
- Monitoring and Logging: Tracking application and infrastructure performance in real-time.
- Communication and Collaboration: Ensuring teams share information transparently across the lifecycle.
- Automated Testing: Using devops tools to run tests automatically at every stage.
By mastering these, you create a “pipeline” where code flows from an idea to a live product. But without security woven into this pipe, you’re essentially building a high-speed highway without any guardrails.
The Hidden Crisis: Why DevSecOps Is Failing in 2026
One of the biggest 2026 realities is that DevSecOps is not failing because of a lack of tools. It’s failing because of fragmented implementation. As LevelAct points out, “DevSecOps broken 2026” is becoming a serious concern as organizations struggle to keep security aligned with rapidly evolving development pipelines.
The core issue? Tool-driven DevSecOps creates workflow fragmentation.
Your developers code in one environment, security scans run in another, CI/CD pipelines live somewhere else, and observability tools sit in a separate stack. Each system may work on its own, but the actual workflow becomes a maze of:
- Context switching
- Delayed feedback
- Missed handoffs
- Slow remediation cycles
Think about your current pipeline: are your teams working in one connected feedback loop, or bouncing between dashboards just to understand one vulnerability?
That’s why simply “adding more security tools” rarely fixes the problem.
The AI Amplification Problem
Now add AI-assisted development into the mix, and the challenge scales fast. Sonatype notes that teams using AI coding assistants write code faster, reduce manual effort, and streamline workflows. But that acceleration introduces a serious multiplier effect: more code, more dependencies, and more potential vulnerabilities entering the system.
The numbers are hard to ignore. Earlier research highlighted by The Silicon Review found that 62% of AI-generated source code contains security vulnerabilities or dangerous design flaws.
Why does this matter to you?
Because traditional AppSec pipelines were not designed for:
- This code volume
- This dependency sprawl
- This speed of generation
- This level of insecure pattern repetition
In other words, AI can boost productivity, but without modern guardrails, it can also scale your security debt.
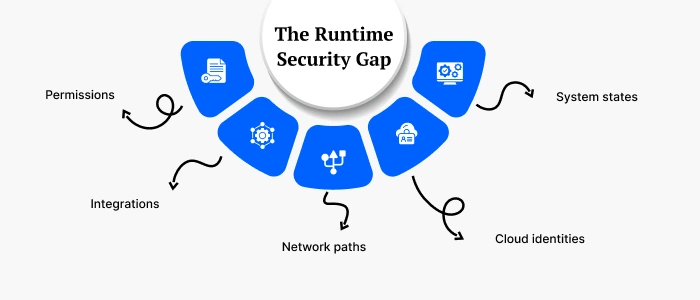
The Runtime Security Gap
Here’s where many DevSecOps strategies completely miss the mark: they focus heavily on build-time security while ignoring runtime vulnerabilities.
As DevOps.com explains, the fundamental flaw is that many pipelines fail at runtime security, not build-time security, when deployed configurations, identities, and infrastructure changes drift from what was validated during testing.
This matters because production traffic exercises real:
- Permissions
- Integrations
- Network paths
- Cloud identities
- System states
These conditions are rarely replicated perfectly in staging.
For example:
- Your SAST tool may catch an injection flaw in development.
- Your SCA tool may flag a vulnerable dependency before release.
- But neither will catch an IAM misconfiguration that exposes your production database to the public internet.
That’s the runtime gap—and it’s one of the most expensive blind spots in modern software delivery.
The 2026 DevSecOps Architecture That Actually Works
So what should you actually implement if you want security without delivery friction? Based on current industry patterns and measurable ROI outcomes, the most effective approach is a layered DevSecOps architecture.
Layer 1: Commit-Time Enforcement (Developer Workstation)
Keep checks lightweight and fast. Your pre-commit hooks should typically complete in under 5 seconds.
- Gitleaks for secrets detection
- Semgrep for baseline SAST patterns
- Checkov for Infrastructure-as-Code (IaC) misconfigurations
Layer 2: Build-Time Deep Analysis (CI Pipeline)
This is where you run broader, deeper automated analysis.
- Static Application Security Testing (SAST): CodeQL, SonarQube, Bandit for Python, or ESLint Security for JavaScript
- Software Composition Analysis (SCA): Snyk, Dependabot, FOSSA, and Syft for SBOM generation
- Container Security: Trivy, Cosign, and OPA/Conftest
Layer 3: Deployment-Time Validation (Staging)
Before production, validate what your software actually does in a running environment.
- Dynamic Application Security Testing (DAST): OWASP ZAP, Burp Suite Enterprise, Nuclei
- Infrastructure Security: Prowler, ScoutSuite, Falco
Layer 4: Production Monitoring (Runtime)
You need continuous visibility after release—not just before it.
- Continuous Security Monitoring: Datadog Security Monitoring, Sysdig Secure, AWS GuardDuty, or Azure Sentinel
Quick gut check: if your visibility stops at the CI pipeline, are you really securing production—or just securing builds?
Implementation Strategy: The Practical Roadmap
If you try to roll out everything at once, you’ll probably create alert fatigue and resistance. A phased approach works better.
Phase 1: Foundation (Weeks 1-4)
Start with the basics that catch high-risk issues early.
- Deploy Gitleaks for secrets detection
- Add baseline SAST
- Establish severity thresholds
- Define ownership for remediation
Phase 2: Pipeline Integration (Weeks 5-8)
Strengthen your automated gates without overwhelming developers.
- Add dependency scanning with Snyk
- Introduce container scanning with Trivy
- Integrate security results into your existing CI workflow
- Begin reporting on trend lines, not just raw findings
Phase 3: Advanced Automation (Weeks 9-12)
This is where your pipeline gets smarter and more policy-driven.
- Deploy DAST in staging
- Implement policy-as-code with OPA/Conftest
- Add IaC validation rules
- Reduce manual review bottlenecks
Phase 4: Production Hardening (Weeks 13-16)
Close the loop by extending security into runtime.
- Add runtime protection with Falco
- Generate and track SBOMs
- Improve production anomaly detection
- Formalize incident response workflows
The ROI Framework: Measuring Success Beyond Tool Deployment
One of the biggest mistakes teams make is measuring success by tool installation instead of business outcomes. As Scadea puts it, “FTE reduction captures, at best, a third of the actual value” of security automation.
So what should you measure instead?
Direct Cost Savings
- Reduced incident response costs
- Lower compliance overhead
- Fewer production security outages
The average breach cost is often cited around $4.45M, which makes prevention and faster detection financially significant.
Velocity Improvements
- Faster security reviews
- Less context switching
- Shorter remediation cycles
- More predictable releases
Risk Reduction
- Lower breach probability
- Better audit readiness
- Stronger supply chain visibility
- Improved compliance posture
Real-World ROI Data
- CrowdStrike reported 264% ROI over three years
- US Tech Automations reports $640k–$920k annual value for mid-market companies
For most organizations, the real return is not just lower headcount effort. It’s the combination of reduced risk, improved delivery velocity, and stronger customer trust.
Common Implementation Pitfalls
Even strong DevSecOps programs can stall if execution gets messy. The most common mistakes include:
- Tool Overload
Adding too many scanners too quickly creates alert fatigue and fragmented workflows. - False Positive Overwhelm
If developers see low-value findings every day, they start ignoring everything—including critical issues. - Lack of Developer Buy-In
If security feels like a blocker instead of an enabler, teams will work around it. - Runtime Blindness
Ignoring production vulnerabilities leaves a dangerous gap between what was tested and what is actually running.
The goal is not maximum tooling. The goal is high-signal security integrated into the way your teams already ship software.
The Future of DevSecOps: 2026-2027
The evolution of DevSecOps is moving from a set of integrated tools to an autonomous, context-aware ecosystem. If you’re planning for the next 12–18 months, the shift is clear: security is becoming more adaptive, more intelligent, and far more embedded in how software gets built and shipped.
1. From “Shift-Left” to “Shift-Everywhere” (Agentic Security)
We are moving beyond simple shift-left strategies to Agentic Development Security (ADS). This model uses autonomous AI agents that do more than run static scans. They understand business logic, runtime context, and the intent behind code changes.
In practice, that means security controls will be everywhere:
- In the IDE
- In the CI/CD pipeline
- In deployment workflows
- In runtime environments
- In feedback loops that continuously adapt to new risk signals
This is the real transition from isolated security checkpoints to continuous, context-aware protection.
2. Autonomous Security Remediation
The detection-only era is ending. Powered by Reinforcement Learning (RL) and multi-agent systems, the next wave of DevSecOps will focus on autonomous remediation.
Instead of just identifying a vulnerability, AI agents will increasingly be able to:
- Detect the issue
- Draft a fix
- Test the patch in a constrained environment
- Propose remediation in an auditable review loop
This self-healing DevSecOps approach matters because AI coding assistants are generating software at a scale that manual security review simply can’t keep up with.
Ask yourself: if your developers are shipping 5x more code, can your current security process realistically review 5x more risk?
3. Global Supply Chain Mandates (The SBOM Era)
Software Bills of Materials (SBOMs) are no longer optional. The EU Cyber Resilience Act (CRA) and updated US CISA/NIST guidance are pushing supply chain transparency into baseline compliance territory.
Key milestones organizations should be preparing for include:
- September 2026: Mandatory reporting of actively exploited vulnerabilities within 24 hours becomes standard in many markets
- December 2027: Full SBOM compliance across digital products in the EU, with significant penalties for non-compliance
To stay ahead, teams should standardize on formats such as:
- CycloneDX (v1.6+)
- SPDX (v3.0.1+)
If you’re still treating SBOM generation as a side task, that’s a risk—not just a tooling gap.
4. The AI Velocity Gap and Security Debt
AI coding assistants have created what many teams are now feeling as the AI Velocity Gap. Developers may be 5x more productive, while security teams are often still staffed and structured around traditional operating ratios like 1:100.
That imbalance creates a dangerous result: security debt accumulates faster than teams can triage it.
The future response is not simply “hire more reviewers.” It’s to embed:
- AI-driven policy enforcement
- Prompt-level security guardrails
- Orchestration-layer validation
- Automated risk scoring at machine speed
In short, security has to scale at the same speed as code generation—or it becomes the bottleneck and the blind spot at the same time.
5. Identity-Centric Cloud Risk
Cloud risk is also shifting. In 2026–2027, many of the most serious exposures will be design-driven rather than disruption-driven. The biggest concern is no longer just whether a server is patched. It’s whether your identity model and permission graph quietly allow privilege escalation.
The new primary attack surfaces include:
- Misconfigured IAM policies
- Over-permissive service roles
- Delegated trust through OAuth
- Excessive machine-to-machine access
- Hidden reachability paths across cloud resources
That’s why mature DevSecOps teams are adopting Cloud Infrastructure Entitlement Management (CIEM) to map entitlement sprawl, analyze reachability paths, and block risky privilege chains before attackers can exploit them.
6. Platform Engineering for Security-by-Design
Another major shift is the convergence of DevSecOps and Platform Engineering. More organizations are building Internal Developer Platforms (IDPs) that provide secure-by-default workflows instead of expecting every team to reinvent them.
These platforms usually include:
- Standardized golden-path templates
- Pre-vetted infrastructure modules
- Built-in security gates
- Automated policy checks
- Reusable deployment patterns
- Centralized observability and auditability
The benefit is simple: the secure path becomes the easiest path. And when secure-by-design is also low-friction, developer adoption goes up.
Summary: Your Strategic Pivot
In 2026, staying competitive means moving from reactive scanning to proactive, autonomous governance. The future of DevSecOps is not just about better detection. It’s about continuous context, machine-speed enforcement, and security architectures that evolve alongside AI-driven development.
At Sphinx Solutions, we stay at the forefront of these trends by helping clients build resilient, secure-by-design architectures that leverage AI without inheriting unnecessary risk.
Start building your autonomous security roadmap today. The window for manual security oversight is closing fast.
For teams planning ahead, the message is clear: security maturity will increasingly define delivery maturity.
Conclusion: Security as a Competitive Advantage
In 2026, security isn’t about slowing down to be safe—it’s about building the confidence to move fast.
At Sphinx Solutions, we help organizations navigate this complexity through secure custom software development, AI-driven solutions, and end-to-end digital transformation services. Whether you’re modernizing cloud infrastructure, building intelligent platforms, or scaling engineering teams, the right DevSecOps model helps you protect delivery speed instead of sacrificing it.
Start small, measure impact, and scale gradually. Your future team—and your customers—will thank you.
Frequently Asked Questions
What is the difference between DevOps and DevSecOps?
DevOps focuses on speed, collaboration, and operational efficiency across development and operations teams. DevSecOps adds security into that workflow from the beginning, so security becomes part of how you ship software, not a separate approval step at the end.
Why is DevSecOps especially important in 2026?
Because modern threats move faster than traditional remediation cycles. With exploit windows shrinking and AI-assisted development increasing code output, you need security controls that operate continuously across commit-time, build-time, deployment, and runtime.
What is the biggest mistake companies make when implementing DevSecOps?
The biggest mistake is assuming that buying more tools equals better security. In reality, fragmented tooling often creates workflow friction, alert fatigue, and delayed remediation. Effective DevSecOps is about integrated feedback loops, not just tool count.
How do I start implementing DevSecOps without slowing down developers?
Start small and focus on high-signal controls:
- Add secrets scanning like Gitleaks
- Introduce lightweight SAST
- Scan dependencies with SCA tools
- Expand gradually into DAST, policy-as-code, and runtime monitoring
This phased approach helps you improve security posture without overwhelming your engineering team.
Why is runtime security so important?
Because many real-world security failures happen after deployment, when cloud identities, configurations, integrations, and permissions behave differently in production than they did in staging. Build-time checks matter, but they can’t fully replace runtime visibility.
Ready to Secure Your Digital Transformation?
Building secure software without sacrificing release velocity is possible when your workflows, tooling, and teams are aligned. With 15+ years of experience, 200+ in-house experts, 1500+ solutions delivered, and a 99% client retention rate, Sphinx Solutions helps you implement secure, scalable engineering practices that support long-term growth.
Contact our experts today to build a secure software delivery pipeline that actually scales.









 +1 646 500 3924
+1 646 500 3924 +91-20-29701664
+91-20-29701664